Journal Description
Computation
Computation
is a peer-reviewed journal of computational science and engineering published monthly online by MDPI.
- Open Access— free for readers, with article processing charges (APC) paid by authors or their institutions.
- High Visibility: indexed within Scopus, ESCI (Web of Science), CAPlus / SciFinder, Inspec, dblp, and other databases.
- Journal Rank: CiteScore - Q2 (Applied Mathematics)
- Rapid Publication: manuscripts are peer-reviewed and a first decision is provided to authors approximately 16.3 days after submission; acceptance to publication is undertaken in 3.7 days (median values for papers published in this journal in the first half of 2023).
- Recognition of Reviewers: reviewers who provide timely, thorough peer-review reports receive vouchers entitling them to a discount on the APC of their next publication in any MDPI journal, in appreciation of the work done.
Impact Factor:
2.2 (2022);
5-Year Impact Factor:
2.2 (2022)
Latest Articles
Impact of Cross-Tie Material Nonlinearity on the Dynamic Behavior of Shallow Flexible Cable Networks
Computation 2023, 11(9), 169; https://doi.org/10.3390/computation11090169 (registering DOI) - 01 Sep 2023
Abstract
Cross-ties have proven their efficacy in mitigating vibrations in bridge stay cables. Several factors, such as cross-tie malfunctions due to slackening or snapping, as well as the utilization of high-energy dissipative materials, can introduce nonlinear restoring forces in the cross-ties. While previous studies
[...] Read more.
Cross-ties have proven their efficacy in mitigating vibrations in bridge stay cables. Several factors, such as cross-tie malfunctions due to slackening or snapping, as well as the utilization of high-energy dissipative materials, can introduce nonlinear restoring forces in the cross-ties. While previous studies have investigated the influence of the former on cable network dynamics, the evaluation of the impact of nonlinear cross-tie materials remains unexplored. In this current research, an existing analytical model of a two-shallow-flexible-cable network has been extended to incorporate the cross-tie material nonlinearity in the formulation. The harmonic balance method (HBM) is employed to determine the equivalent linear stiffness of the cross-ties. The dynamic response of a cable network containing nonlinear cross-ties is approximated by comparing it to an equivalent linear system. Additionally, the study delves into the effects of the cable vibration amplitude, cross-tie material properties, installation location, and the length ratio between constituent cables on both the fundamental frequency of the cable network and the equivalent linear stiffness of the cross-ties. The findings reveal that the presence of cross-tie nonlinearity significantly influences the in-plane modal response of the cable network. Not only the frequencies of all the modes are reduced, but the formation of local modes is delayed to a high order. In contrast to an earlier finding based on a linear cross-tie assumption, with nonlinearity present, moving a cross-tie towards the mid-span of a cable would not enhance the in-plane stiffness of the network. Moreover, the impact of the length ratio on the network in-plane stiffness and frequency is contingent on its combined effect on the cross-tie axial stiffness and the lateral stiffness of neighboring cables.
Full article
(This article belongs to the Special Issue 10th Anniversary of Computation—Computational Engineering)
►
Show Figures
Open AccessArticle
Adapting PINN Models of Physical Entities to Dynamical Data
Computation 2023, 11(9), 168; https://doi.org/10.3390/computation11090168 (registering DOI) - 01 Sep 2023
Abstract
This article examines the possibilities of adapting approximate solutions of boundary value problems for differential equations using physics-informed neural networks (PINNs) to changes in data about the physical entity being modelled. Two types of models are considered: PINN and parametric PINN (PPINN). The
[...] Read more.
This article examines the possibilities of adapting approximate solutions of boundary value problems for differential equations using physics-informed neural networks (PINNs) to changes in data about the physical entity being modelled. Two types of models are considered: PINN and parametric PINN (PPINN). The former is constructed for a fixed parameter of the problem, while the latter includes the parameter for the number of input variables. The models are tested on three problems. The first problem involves modelling the bending of a cantilever rod under varying loads. The second task is a non-stationary problem of a thermal explosion in the plane-parallel case. The initial model is constructed based on an ordinary differential equation, while the modelling object satisfies a partial differential equation. The third task is to solve a partial differential equation of mixed type depending on time. In all cases, the initial models are adapted to the corresponding pseudo-measurements generated based on changing equations. A series of experiments are carried out for each problem with different functions of a parameter that reflects the character of changes in the object. A comparative analysis of the quality of the PINN and PPINN models and their resistance to data changes has been conducted for the first time in this study.
Full article
(This article belongs to the Special Issue 10th Anniversary of Computation—Computational Engineering)
►▼
Show Figures
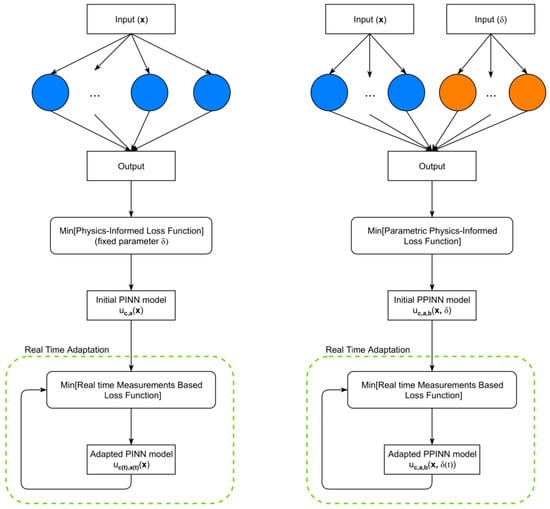
Figure 1
Open AccessArticle
Numerical Computation of Hydrodynamic Characteristics of an Automated Hand-Washing System
Computation 2023, 11(9), 167; https://doi.org/10.3390/computation11090167 - 22 Aug 2023
Abstract
The aim of this study is to develop a physical model and investigate the bactericidal effect of an automated hand-washing system through numerical computation, which is essential in areas affected by COVID-19 to ensure safety and limit the spread of the pandemic. The
[...] Read more.
The aim of this study is to develop a physical model and investigate the bactericidal effect of an automated hand-washing system through numerical computation, which is essential in areas affected by COVID-19 to ensure safety and limit the spread of the pandemic. The computational fluid dynamics approach is used to study the movement of the solution inside the hand-washing chamber. The finite element method with the k-
(This article belongs to the Section Computational Engineering)
►▼
Show Figures
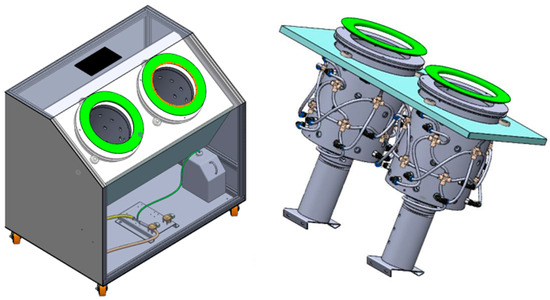
Figure 1
Open AccessArticle
Evolutionary PINN Learning Algorithms Inspired by Approximation to Pareto Front for Solving Ill-Posed Problems
by
, , , , and
Computation 2023, 11(8), 166; https://doi.org/10.3390/computation11080166 - 21 Aug 2023
Abstract
The article presents the development of new physics-informed evolutionary neural network learning algorithms. These algorithms aim to address the challenges of ill-posed problems by constructing a population close to the Pareto front. The study focuses on comparing the algorithm’s capabilities based on three
[...] Read more.
The article presents the development of new physics-informed evolutionary neural network learning algorithms. These algorithms aim to address the challenges of ill-posed problems by constructing a population close to the Pareto front. The study focuses on comparing the algorithm’s capabilities based on three quality criteria of solutions. To evaluate the algorithms’ performance, two benchmark problems have been used. The first involved solving the Laplace equation in square regions with discontinuous boundary conditions. The second problem considered the absence of boundary conditions but with the presence of measurements. Additionally, the study investigates the influence of hyperparameters on the final results. Comparisons have been made between the proposed algorithms and standard algorithms for constructing neural networks based on physics (commonly referred to as vanilla’s algorithms). The results demonstrate the advantage of the proposed algorithms in achieving better performance when solving incorrectly posed problems. Furthermore, the proposed algorithms have the ability to identify specific solutions with the desired smoothness.
Full article
(This article belongs to the Special Issue 10th Anniversary of Computation—Computational Engineering)
►▼
Show Figures
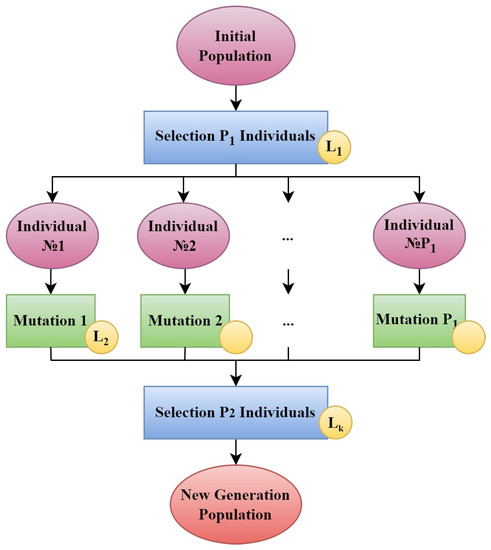
Figure 1
Open AccessArticle
Investigation of the Failure Response of Masonry Walls Subjected to Blast Loading Using Nonlinear Finite Element Analysis
Computation 2023, 11(8), 165; https://doi.org/10.3390/computation11080165 - 21 Aug 2023
Abstract
A numerical investigation of masonry walls subjected to blast loads is presented in this article. A non-linear finite element model is proposed to describe the structural response of the walls. A unilateral contact–friction law is used in the interfaces of the masonry blocks
[...] Read more.
A numerical investigation of masonry walls subjected to blast loads is presented in this article. A non-linear finite element model is proposed to describe the structural response of the walls. A unilateral contact–friction law is used in the interfaces of the masonry blocks to provide the discrete failure between the blocks. A continuum damage plasticity model is also used to account for the compressive and tensile failure of the blocks. The main goal of this article is to investigate the different collapse mechanisms that arise as an effect of the blast load parameters and the static load of the wall. Parametric studies are conducted to evaluate the effect of the blast source–wall (standoff) distance and the blast weight on the structural response of the system. It is shown that the traditional in-plane diagonal cracking failure mode may still dominate when a blast action is present, depending on the considered standoff distance and the blast weight when in-plane static loading is also applied to the wall. It is also highlighted that the presence of an opening in the wall may significantly reduce the effect of the blasting action.
Full article
(This article belongs to the Special Issue Computational Methods in Structural Engineering)
►▼
Show Figures
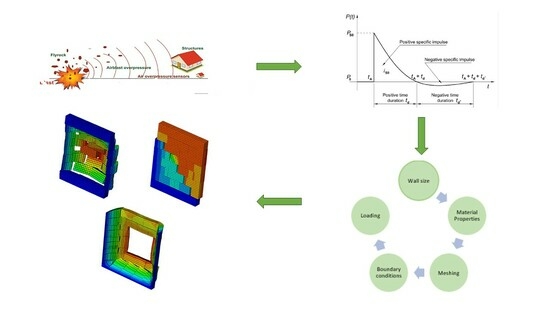
Graphical abstract
Open AccessArticle
Diffusion Kinetics Theory of Removal of Assemblies’ Surface Deposits with Flushing Oil
Computation 2023, 11(8), 164; https://doi.org/10.3390/computation11080164 - 20 Aug 2023
Abstract
The diffusion kinetics theory of cleaning assemblies such as combustion engines with flushing oil has been introduced. Evolution of tar deposits on the engine surfaces and in the lube system has been described through the erosion dynamics. The time-dependent concentration pattern related to
[...] Read more.
The diffusion kinetics theory of cleaning assemblies such as combustion engines with flushing oil has been introduced. Evolution of tar deposits on the engine surfaces and in the lube system has been described through the erosion dynamics. The time-dependent concentration pattern related to hydrodynamic (sub)layers around the tar deposit has been uncovered. Nonlinear equations explaining the experimentally observed dependences for scouring the contaminants off with the oil have been derived and indicate the power law in time. For reference purposes, a similar analysis based on formal chemical kinetics has been accomplished. Factors and scouring parameters for the favor of either mechanism have been discussed. Any preference for either diffusion or chemical kinetics should be based on a careful selection of washing agents in the flushing oil. Future directions of studies are proposed.
Full article
(This article belongs to the Special Issue Mathematical Modeling and Study of Nonlinear Dynamic Processes)
►▼
Show Figures
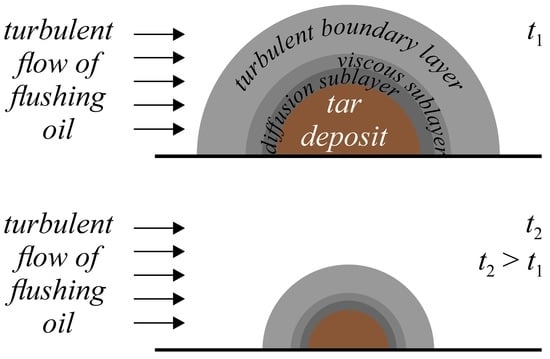
Graphical abstract
Open AccessArticle
Quadrotor Trajectory Tracking Using Model Reference Adaptive Control, Neural Network-Based Parameter Uncertainty Compensator, and Different Plant Parameterizations
Computation 2023, 11(8), 163; https://doi.org/10.3390/computation11080163 - 18 Aug 2023
Abstract
A quadrotor trajectory tracking problem is addressed via the design of a model reference adaptive control (MRAC) system. As for real-world applications, the entire quadrotor dynamics is typically unknown. To take that into account, we consider a plant model, which contains uncertain nonlinear
[...] Read more.
A quadrotor trajectory tracking problem is addressed via the design of a model reference adaptive control (MRAC) system. As for real-world applications, the entire quadrotor dynamics is typically unknown. To take that into account, we consider a plant model, which contains uncertain nonlinear terms resulting from aerodynamic friction, blade flapping, and the fact that the mass and inertia moments of the quadrotor may change from their nominal values. Unlike many known studies, the explicit equations of the parameter uncertainty for the position control loop are derived in two different ways using the differential flatness approach: the control signals are (i) used and (ii) not used in the parametric uncertainty parameterization. After analysis, the neural network (NN) is chosen for both cases as a compensator of such uncertainty, and the set of NN input signals is justified for each of them. Unlike many known MRAC systems with NN for quadrotors, in this study, we use the
(This article belongs to the Special Issue Control Systems, Mathematical Modeling and Automation II)
►▼
Show Figures

Figure 1
Open AccessArticle
The Complexity of the Super Subdivision of Cycle-Related Graphs Using Block Matrices
Computation 2023, 11(8), 162; https://doi.org/10.3390/computation11080162 - 15 Aug 2023
Abstract
The complexity (number of spanning trees) in a finite graph
The complexity (number of spanning trees) in a finite graph
(This article belongs to the Special Issue 10th Anniversary of Computation—Computational Engineering)
►▼
Show Figures
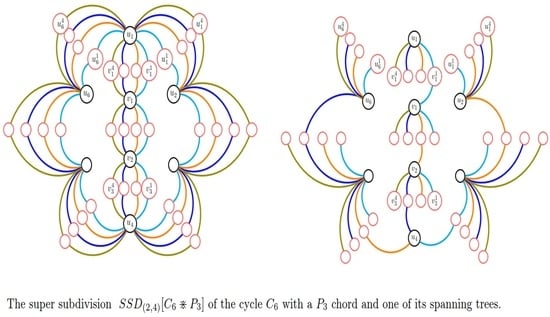
Graphical abstract
Open AccessArticle
Study on Optical Positioning Using Experimental Visible Light Communication System
by
, , , , , and
Computation 2023, 11(8), 161; https://doi.org/10.3390/computation11080161 - 14 Aug 2023
Abstract
Visible light positioning systems (VLP) have attracted significant commercial and research interest because of the many advantages they possess over other applications such as radio frequency (RF) positioning systems. In this work, an experimental configuration of an indoor VLP system based on the
[...] Read more.
Visible light positioning systems (VLP) have attracted significant commercial and research interest because of the many advantages they possess over other applications such as radio frequency (RF) positioning systems. In this work, an experimental configuration of an indoor VLP system based on the well-known Lambertian light emission, is investigated. The corresponding results are also presented, and show that the system retains high enough accuracy to be operational, even in cases of low transmitted power and high background noise.
Full article
(This article belongs to the Special Issue 10th Anniversary of Computation—Computational Engineering)
►▼
Show Figures
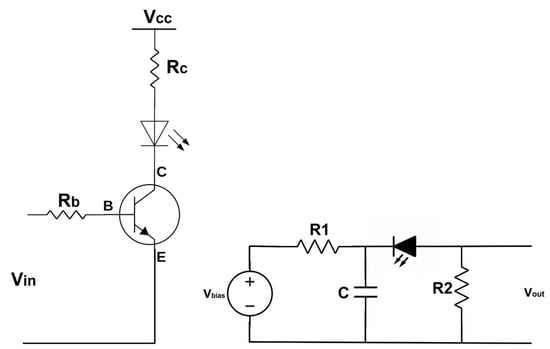
Figure 1
Open AccessArticle
Analysis and 3D Imaging of Multidimensional Complex THz Fields and 3D Diagnostics Using 3D Visualization via Light Field
by
, , , , and
Computation 2023, 11(8), 160; https://doi.org/10.3390/computation11080160 - 14 Aug 2023
Abstract
We present a numerical platform for 3D imaging and general analysis of multidimensional complex THz fields. A special 3D visualization is obtained by converting electromagnetic (EM) radiation to a light field via the Wigner distribution function, which is known for discovering (revealing) hidden
[...] Read more.
We present a numerical platform for 3D imaging and general analysis of multidimensional complex THz fields. A special 3D visualization is obtained by converting electromagnetic (EM) radiation to a light field via the Wigner distribution function, which is known for discovering (revealing) hidden details. This allows for 3D diagnostics using the simple techniques of geometrical optics, which significantly facilitates the whole analysis. This simulation was applied to a complex field composed of complex beams emitted as ultra-narrow femtosecond pulses. A method was developed for the generation of phase–amplitude and spectral characteristics of complex multimode radiation in a free-electron laser (FEL) operating under various parameters. The tool was successful at diagnosing an early design of the transmission line (TL) of an innovative accelerator at the Schlesinger Family Center for Compact Accelerators, Radiation Sources, and Applications.
Full article
(This article belongs to the Special Issue Intelligent Computing, Modeling and its Applications)
►▼
Show Figures
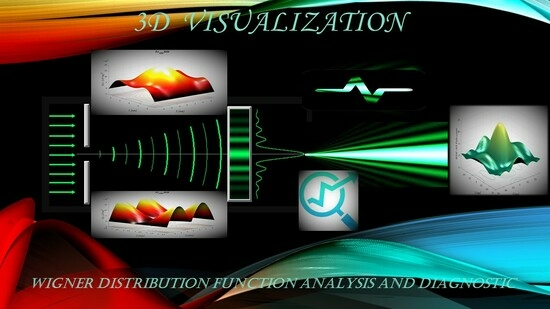
Graphical abstract
Open AccessArticle
Sensitivity Analysis of Mathematical Models
by
Computation 2023, 11(8), 159; https://doi.org/10.3390/computation11080159 - 14 Aug 2023
Abstract
►▼
Show Figures
The construction of a mathematical model of a complicated system is often associated with the evaluation of inputs’ (arguments, factors) influence on the output (response), the identification of important relationships between the variables used, and reduction of the model by decreasing the number
[...] Read more.
The construction of a mathematical model of a complicated system is often associated with the evaluation of inputs’ (arguments, factors) influence on the output (response), the identification of important relationships between the variables used, and reduction of the model by decreasing the number of its inputs. These tasks are related to the problems of Sensitivity Analysis of mathematical models. The author proposes an alternative approach based on applying Analysis of Finite Fluctuations that uses the Lagrange mean value theorem to estimate the contribution of changes to the variables of a function to the output change. The article investigates the presented approach on an example of a class of fully connected neural network models. As a result of Sensitivity Analysis, a set of sensitivity measures for each input is obtained. For their averaging, it is proposed to use a point-and-interval estimation algorithm using Tukey’s weighted average. The comparison of the described method with the computation of Sobol’s indices is given; the consistency of the proposed method is shown. The computational robustness of the procedure for finding sensitivity measures of inputs is investigated. Numerical experiments are carried out on the neuraldat data set of the NeuralNetTools library of the R data processing language and on data of the healthcare services provided in the Lipetsk region.
Full article

Figure 1
Open AccessArticle
Genomic Phylogeny Using the MaxwellTM Classifier Based on Burrows–Wheeler Transform
by
, , , , and
Computation 2023, 11(8), 158; https://doi.org/10.3390/computation11080158 - 11 Aug 2023
Abstract
Background: In present genomes, current relics of a circular RNA appear which could have played a central role as a primitive catalyst of the peptide genesis. Methods: Using a proximity measure to this circular RNA and the distance, a new unsupervised classifier called
[...] Read more.
Background: In present genomes, current relics of a circular RNA appear which could have played a central role as a primitive catalyst of the peptide genesis. Methods: Using a proximity measure to this circular RNA and the distance, a new unsupervised classifier called MaxwellTM has been constructed based on the Burrows–Wheeler transform algorithm. Results: By applying the classifier to numerous genomes from various realms (Bacteria, Archaea, Vegetables and Animals), we obtain phylogenetic trees that are coherent with biological trees based on pure evolutionary arguments. Discussion: We discuss the role of the combinatorial operators responsible for the evolution of the genome of many species. Conclusions: We opened up possibilities for understanding the mechanisms of a primitive factory of peptides represented by an RNA ring. We showed that this ring was able to transmit some of its sub-sequences in the sequences of genes involved in the mechanisms of the current ribosomal production of proteins.
Full article
(This article belongs to the Special Issue 10th Anniversary of Computation—Computational Biology)
►▼
Show Figures
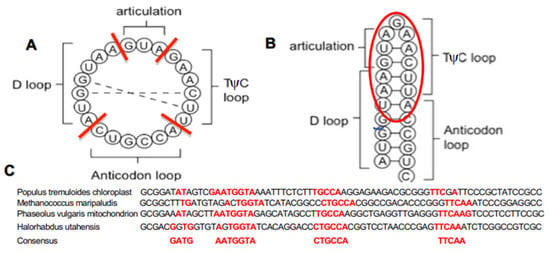
Figure 1
Open AccessArticle
The Generalised Reissner–Nordstrom Spacetimes, the Cosmological Constant and the Linear Term
Computation 2023, 11(8), 157; https://doi.org/10.3390/computation11080157 - 11 Aug 2023
Abstract
►▼
Show Figures
The Reissner–Nordstrom spacetimes and some generalised Reissner–Nordstrom spacetimes are analysed. The blackhole solutions are considered. The generalised Reissner–Nordstrom spacetimes with a cosmological-constant term, endowed with a Schwarzschild solid-angle element, are analytically delineated: the radii of the blackholes are analytically calculated and newly parameterised;
[...] Read more.
The Reissner–Nordstrom spacetimes and some generalised Reissner–Nordstrom spacetimes are analysed. The blackhole solutions are considered. The generalised Reissner–Nordstrom spacetimes with a cosmological-constant term, endowed with a Schwarzschild solid-angle element, are analytically delineated: the radii of the blackholes are analytically calculated and newly parameterised; the coordinate-singularity-avoiding coordinate extension is newly found, i.e., such that the tortoise-coordinate transformation can therefore be applied; the new conditions for merging the solutions as the physical horizons are analytically outlined; the new parameter space of the model is set and constrained; the new role of the cosmological-constant term in designating the Schwarzschild radius is demonstrated; the Reissner–Nordstrom–deSitter case and in the Reissner–Nordstrom–anti-deSitter one are newly demonstrated to be characterised in a different analytical manner. Furthermore, a new family of solutions is found, qualified after the cosmological-constant term. The generalised Reissner–Nordstrom spacetimes with a linear term, endowed with a Schwarzschild solid-angle element, are analytically studied: the radii are enumerated and newly parameterised; the new conditions for the merging of the radii as the physical horizons are set; the new parameter space of the system is arranged and constrained; the role of the linear-term parameter in the delineation of the Schwarzschild radius is newly proven to be apt to imply a small modification only. The generalised Reissner–Nordstrom spacetimes, endowed with a Schwarzschild solid-angle element, with a linear term and a cosmological-constant term are newly inspected: the radii are analytically calculated and newly parameterised; the new conditions for the merging of the radii as the physical horizons are prescribed; the new parameter space of the scheme is appointed and constrained; the roles of the parameters are newly scrutinised in their application to modify the physical interpretation of the Reissner–Nordstrom parameters only in a small manner; the coordinate-singularity-avoiding coordinate extensions are newly found, i.e., such that the tortoise-coordinate transformation can therefore be applied; the definition of the physical radii is newly found; the results are newly demonstrated in both cases of a positive value of the cosmological constant and in the case of a negative value of the cosmological constant in a different manner; the role of the linear-term parameter is also newly enunciated. More over, a new family of solutions is found, which is delineated after particular values of the linear term and of the cosmological-constant one. The quantum implementation of the models is prospectively envisaged.
Full article

Figure 1
Open AccessArticle
CEAT: Categorising Ethereum Addresses’ Transaction Behaviour with Ensemble Machine Learning Algorithms
by
, , and
Computation 2023, 11(8), 156; https://doi.org/10.3390/computation11080156 - 09 Aug 2023
Abstract
Cryptocurrencies are rapidly growing and are increasingly accepted by major commercial vendors. However, along with their rising popularity, they have also become the go-to currency for illicit activities driven by the anonymity they provide. Cryptocurrencies such as the one on the Ethereum blockchain
[...] Read more.
Cryptocurrencies are rapidly growing and are increasingly accepted by major commercial vendors. However, along with their rising popularity, they have also become the go-to currency for illicit activities driven by the anonymity they provide. Cryptocurrencies such as the one on the Ethereum blockchain provide a way for entities to hide their real-world identities behind pseudonyms, also known as addresses. Hence, the purpose of this work is to uncover the level of anonymity in Ethereum by investigating multiclass classification models for Externally Owned Accounts (EOAs) of Ethereum. The researchers aim to achieve this by examining patterns of transaction activity associated with these addresses. Using a labelled Ethereum address dataset from Kaggle and the Ethereum crypto dataset by Google BigQuery, an address profiles dataset was compiled based on the transaction history of the addresses. The compiled dataset, consisting of 4371 samples, was used to tune and evaluate the Random Forest, Gradient Boosting and XGBoost classifier for predicting the category of the addresses. The best-performing model found for the problem was the XGBoost classifier, achieving an accuracy of 75.3% with a macro-averaged F1-Score of 0.689. Following closely was the Random Forest classifier, with an accuracy of 73.7% and a macro-averaged F1-Score of 0.641. Gradient Boosting came in last with 73% accuracy and a macro-averaged F1-Score of 0.659. Owing to the data limitations in this study, the overall scores of the best model were weaker in comparison to similar research, with the exception of precision, which scored slightly higher. Nevertheless, the results proved that it is possible to predict the category of an Ethereum wallet address such as Phish/Hack, Scamming, Exchange and ICO wallets based on its transaction behaviour.
Full article
(This article belongs to the Special Issue Intelligent Computing, Modeling and its Applications)
►▼
Show Figures
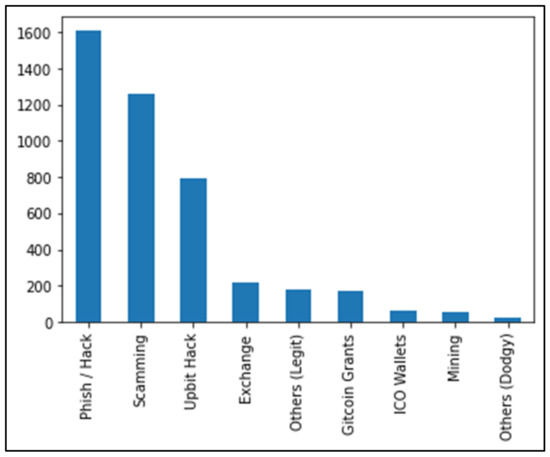
Figure 1
Open AccessArticle
A Parametric Family of Triangular Norms and Conorms with an Additive Generator in the Form of an Arctangent of a Linear Fractional Function
Computation 2023, 11(8), 155; https://doi.org/10.3390/computation11080155 - 08 Aug 2023
Abstract
At present, fuzzy modeling has established itself as an effective tool for designing and developing systems for various purposes that are used to solve problems of control, diagnostics, forecasting, and decision making. One of the most important problems is the choice and justification
[...] Read more.
At present, fuzzy modeling has established itself as an effective tool for designing and developing systems for various purposes that are used to solve problems of control, diagnostics, forecasting, and decision making. One of the most important problems is the choice and justification of an appropriate functional representation of the main fuzzy operations. It is known that, in the class of rational functions, such operations can be represented by additive generators in the form of a linear fractional function, a logarithm of a linear fractional function, and an arctangent of a linear fractional function. The paper is devoted to the latter case. Restrictions on the parameters, under which the arctangent of a linear fractional function is an increasing or decreasing generator, are defined. For each case, a corresponding fuzzy operation (a triangular norm or a conorm) is constructed. The theoretical significance of the research results lies in the fact that the obtained parametric families enrich the theory of Archimedean triangular norms and conorms and provide additional opportunities for the functional representation of fuzzy operations in the framework of fuzzy modeling. In addition, in fact, we formed a scheme for study functions that can be considered additive generators and constructed the corresponding fuzzy operations.
Full article
(This article belongs to the Special Issue Control Systems, Mathematical Modeling and Automation II)
►▼
Show Figures

Figure 1
Open AccessArticle
Revealing the Genetic Code Symmetries through Computations Involving Fibonacci-like Sequences and Their Properties
Computation 2023, 11(8), 154; https://doi.org/10.3390/computation11080154 - 07 Aug 2023
Abstract
In this work, we present a new way of studying the mathematical structure of the genetic code. This study relies on the use of mathematical computations involving five Fibonacci-like sequences; a few of their “seeds” or “initial conditions” are chosen according to the
[...] Read more.
In this work, we present a new way of studying the mathematical structure of the genetic code. This study relies on the use of mathematical computations involving five Fibonacci-like sequences; a few of their “seeds” or “initial conditions” are chosen according to the chemical and physical data of the three amino acids serine, arginine and leucine, playing a prominent role in a recent symmetry classification scheme of the genetic code. It appears that these mathematical sequences, of the same kind as the famous Fibonacci series, apart from their usual recurrence relations, are highly intertwined by many useful linear relationships. Using these sequences and also various sums or linear combinations of them, we derive several physical and chemical quantities of interest, such as the number of total coding codons, 61, obeying various degeneracy patterns, the detailed number of H/CNOS atoms and the integer molecular mass (or nucleon number), in the side chains of the coded amino acids and also in various degeneracy patterns, in agreement with those described in the literature. We also discover, as a by-product, an accurate description of the very chemical structure of the four ribonucleotides uridine monophosphate (UMP), cytidine monophosphate (CMP), adenosine monophosphate (AMP) and guanosine monophosphate (GMP), the building blocks of RNA whose groupings, in three units, constitute the triplet codons. In summary, we find a full mathematical and chemical connection with the “ideal sextet’s classification scheme”, which we alluded to above, as well as with others—notably, the Findley–Findley–McGlynn and Rumer’s symmetrical classifications.
Full article
(This article belongs to the Special Issue Computations in Mathematics, Mathematical Education, and Science)
Open AccessArticle
Uncoupling Techniques for Multispecies Diffusion–Reaction Model
Computation 2023, 11(8), 153; https://doi.org/10.3390/computation11080153 - 04 Aug 2023
Abstract
►▼
Show Figures
We consider the multispecies model described by a coupled system of diffusion–reaction equations, where the coupling and nonlinearity are given in the reaction part. We construct a semi-discrete form using a finite volume approximation by space. The fully implicit scheme is used for
[...] Read more.
We consider the multispecies model described by a coupled system of diffusion–reaction equations, where the coupling and nonlinearity are given in the reaction part. We construct a semi-discrete form using a finite volume approximation by space. The fully implicit scheme is used for approximation by time, which leads to solving the coupled nonlinear system of equations at each time step. This paper presents two uncoupling techniques based on the explicit–implicit scheme and the operator-splitting method. In the explicit–implicit scheme, we take the concentration of one species in coupling term from the previous time layer to obtain a linear uncoupled system of equations. The second approach is based on the operator-splitting technique, where we first solve uncoupled equations with the diffusion operator and then solve the equations with the local reaction operator. The stability estimates are derived for both proposed uncoupling schemes. We present a numerical investigation for the uncoupling techniques with varying time step sizes and different scales of the diffusion coefficient.
Full article

Figure 1
Open AccessArticle
Enhancing the Hardware Pipelining Optimization Technique of the SHA-3 via FPGA
by
and
Computation 2023, 11(8), 152; https://doi.org/10.3390/computation11080152 - 03 Aug 2023
Abstract
►▼
Show Figures
Information is transmitted between multiple insecure routing hops in text, image, video, and audio. Thus, this multi-hop digital data transfer makes secure transmission with confidentiality and integrity imperative. This protection of the transmitted data can be achieved via hashing algorithms. Furthermore, data integrity
[...] Read more.
Information is transmitted between multiple insecure routing hops in text, image, video, and audio. Thus, this multi-hop digital data transfer makes secure transmission with confidentiality and integrity imperative. This protection of the transmitted data can be achieved via hashing algorithms. Furthermore, data integrity must be ensured, which is feasible using hashing algorithms. The advanced cryptographic Secure Hashing Algorithm 3 (SHA-3) is not sensitive to a cryptanalysis attack and is widely preferred due to its long-term security in various applications. However, due to the ever-increasing size of the data to be transmitted, an effective improvement is required to fulfill real-time computations with multiple types of optimization. The use of FPGAs is the ideal mechanism to improve algorithm performance and other metrics, such as throughput (Gbps), frequency (MHz), efficiency (Mbps/slices), reduction of area (slices), and power consumption. Providing upgraded computer architectures for SHA-3 is an active area of research, with continuous performance improvements. In this article, we have focused on enhancing the hardware performance metrics of throughput and efficiency by reducing the area cost of the SHA-3 for all output size lengths (224, 256, 384, and 512 bits). Our approach introduces a novel architectural design based on pipelining, which is combined with a simplified format for the round constant (RC) generator in the Iota (

Figure 1
Open AccessArticle
Finite Element Analysis of ACL Reconstruction-Compatible Knee Implant Design with Bone Graft Component
Computation 2023, 11(8), 151; https://doi.org/10.3390/computation11080151 - 02 Aug 2023
Abstract
Knee osteoarthritis is a musculoskeletal defect specific to the soft tissues in the knee joint and is a degenerative disease that affects millions of people. Although drug intake can slow down progression, total knee arthroplasty has been the gold standard for the treatment
[...] Read more.
Knee osteoarthritis is a musculoskeletal defect specific to the soft tissues in the knee joint and is a degenerative disease that affects millions of people. Although drug intake can slow down progression, total knee arthroplasty has been the gold standard for the treatment of this disease. This surgical procedure involves replacing the tibiofemoral joint with an implant. The most common implants used for this require the removal of either the anterior cruciate ligament (ACL) alone or both cruciate ligaments which alters the native knee joint mechanics. Bi-cruciate-retaining implants have been developed but not frequently used due to the complexity of the procedure and the occurrences of intraoperative failures such as ACL and tibial eminence rupture. In this study, a knee joint implant was modified to have a bone graft that should aid in ACL reconstruction. The mechanical behavior of the bone graft was studied through finite element analysis (FEA). The results show that the peak Christensen safety factor for cortical bone is 0.021 while the maximum shear stress of the cancellous bone is 3 MPa which signifies that the cancellous bone could fail when subjected to the ACL loads, depending on the graft shear strength which could vary depending on the graft source, while cortical bone could withstand the walking load. It would be necessary to optimize the bone graft geometry for stress distribution as well as to evaluate the effectiveness of bone healing prior to implementation.
Full article
(This article belongs to the Section Computational Engineering)
►▼
Show Figures

Figure 1
Open AccessArticle
The Problem of Effective Evacuation of the Population from Floodplains under Threat of Flooding: Algorithmic and Software Support with Shortage of Resources
by
, , , , and
Computation 2023, 11(8), 150; https://doi.org/10.3390/computation11080150 - 01 Aug 2023
Abstract
Extreme flooding of the floodplains of large lowland rivers poses a danger to the population due to the vastness of the flooded areas. This requires the organization of safe evacuation in conditions of a shortage of temporary and transport resources due to significant
[...] Read more.
Extreme flooding of the floodplains of large lowland rivers poses a danger to the population due to the vastness of the flooded areas. This requires the organization of safe evacuation in conditions of a shortage of temporary and transport resources due to significant differences in the moments of flooding of different spatial parts. We consider the case of a shortage of evacuation vehicles, in which the safe evacuation of the entire population to permanent evacuation points is impossible. Therefore, the evacuation is divided into two stages with the organization of temporary evacuation points on evacuation routes. Our goal is to develop a method for analyzing the minimum resource requirement for the safe evacuation of the population of floodplain territories based on a mathematical model of flood dynamics and minimizing the number of vehicles on a set of safe evacuation schedules. The core of the approach is a numerical hydrodynamic model in shallow water approximation. Modeling the hydrological regime of a real water body requires a multi-layer geoinformation model of the territory with layers of relief, channel structure, and social infrastructure. High-performance computing is performed on GPUs using CUDA. The optimization problem is a variant of the resource investment problem of scheduling theory with deadlines for completing work and is solved on the basis of a heuristic algorithm. We use the results of numerical simulation of floods for the Northern part of the Volga-Akhtuba floodplain to plot the dependence of the minimum number of vehicles that ensure the safe evacuation of the population. The minimum transport resources depend on the water discharge in the Volga river, the start of the evacuation, and the localization of temporary evacuation points. The developed algorithm constructs a set of safe evacuation schedules for the minimum allowable number of vehicles in various flood scenarios. The population evacuation schedules constructed for the Volga-Akhtuba floodplain can be used in practice for various vast river valleys.
Full article
(This article belongs to the Special Issue Control Systems, Mathematical Modeling and Automation II)
►▼
Show Figures

Figure 1

Journal Menu
► ▼ Journal Menu-
- Computation Home
- Aims & Scope
- Editorial Board
- Reviewer Board
- Topical Advisory Panel
- Instructions for Authors
- Special Issues
- Topics
- Sections
- Article Processing Charge
- Indexing & Archiving
- Most Cited & Viewed
- Journal Statistics
- Journal History
- Journal Awards
- Conferences
- Editorial Office
- 10th Anniversary of Computation
Journal Browser
► ▼ Journal BrowserHighly Accessed Articles
Latest Books
E-Mail Alert
News
18 August 2023
Meet Us at the China National Computer Congress 2023 (CNCC 2023), 26–28 October 2023, Shenyang, China
Meet Us at the China National Computer Congress 2023 (CNCC 2023), 26–28 October 2023, Shenyang, China

Topics
Topic in
Axioms, Computation, Dynamics, Mathematics, Symmetry
Structural Stability and Dynamics: Theory and Applications
Topic Editors: Harekrushna Behera, Chia-Cheng Tsai, Jen-Yi ChangDeadline: 30 September 2023
Topic in
Entropy, Algorithms, Computation, MAKE, Energies, Materials
Artificial Intelligence and Computational Methods: Modeling, Simulations and Optimization of Complex Systems
Topic Editors: Jaroslaw Krzywanski, Yunfei Gao, Marcin Sosnowski, Karolina Grabowska, Dorian Skrobek, Ghulam Moeen Uddin, Anna Kulakowska, Anna Zylka, Bachil El FilDeadline: 20 October 2023
Topic in
Applied Sciences, BioMedInformatics, BioTech, Genes, Computation
Computational Intelligence and Bioinformatics (CIB)
Topic Editors: Marco Mesiti, Giorgio Valentini, Elena Casiraghi, Tiffany J. CallahanDeadline: 31 October 2023
Topic in
Entropy, Fractal Fract, Dynamics, Mathematics, Computation, Axioms
Advances in Nonlinear Dynamics: Methods and Applications
Topic Editors: Ravi P. Agarwal, Maria Alessandra RagusaDeadline: 20 November 2023

Conferences
Special Issues
Special Issue in
Computation
Solstice 2023—International Conference on Discrete Models of Complex Systems
Guest Editors: Franco Bagnoli, Anna T. LawniczakDeadline: 15 September 2023
Special Issue in
Computation
Applications of Evolutionary Computation: Past Success and Future Challenges
Guest Editor: Alexandros TzanetosDeadline: 30 September 2023
Special Issue in
Computation
Mathematical Modeling and Study of Nonlinear Dynamic Processes
Guest Editor: Alexander PchelintsevDeadline: 31 October 2023
Special Issue in
Computation
Computational Social Science and Complex Systems
Guest Editors: Minzhang Zheng, Pedro ManriqueDeadline: 15 November 2023



















