-
 Deep Learning and Machine Learning, Better Together Than Apart: A Review on Biometrics Mobile Authentication
Deep Learning and Machine Learning, Better Together Than Apart: A Review on Biometrics Mobile Authentication -
 Mitigating IoT Privacy-Revealing Features by Time Series Data Transformation
Mitigating IoT Privacy-Revealing Features by Time Series Data Transformation -
 Cybersecurity in a Large-Scale Research Facility—One Institution’s Approach
Cybersecurity in a Large-Scale Research Facility—One Institution’s Approach -
 Cybersecurity for AI Systems: A Survey
Cybersecurity for AI Systems: A Survey
Journal Description
Journal of Cybersecurity and Privacy
Journal of Cybersecurity and Privacy
is an international, peer-reviewed, open access journal on all aspects of computer, systems, and information security, published quarterly online by MDPI.
- Open Access— free for readers, with article processing charges (APC) paid by authors or their institutions.
- Rapid Publication: manuscripts are peer-reviewed and a first decision is provided to authors approximately 20 days after submission; acceptance to publication is undertaken in 7.6 days (median values for papers published in this journal in the first half of 2023).
- Recognition of Reviewers: APC discount vouchers, optional signed peer review, and reviewer names published annually in the journal.
- Companion journal: Sensors.
Latest Articles
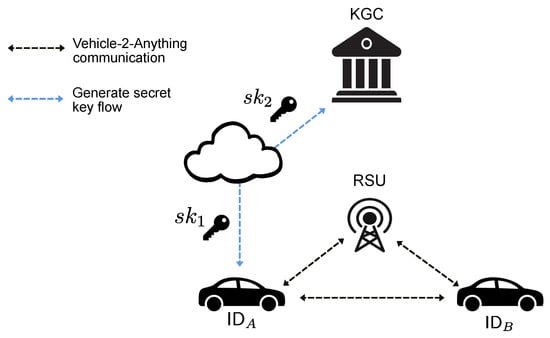
A Gap Analysis of the Adoption Maturity of Certificateless Cryptography in Cooperative Intelligent Transportation Systems
J. Cybersecur. Priv. 2023, 3(3), 591-609; https://doi.org/10.3390/jcp3030028 (registering DOI) - 01 Sep 2023
Abstract
Cooperative Intelligent Transport Systems (C-ITSs) are an important development for society. C-ITSs enhance road safety, improve traffic efficiency, and promote sustainable transportation through interconnected and intelligent communication between vehicles, infrastructure, and traffic-management systems. Many real-world implementations still consider traditional Public Key Infrastructures (PKI)
[...] Read more.
Cooperative Intelligent Transport Systems (C-ITSs) are an important development for society. C-ITSs enhance road safety, improve traffic efficiency, and promote sustainable transportation through interconnected and intelligent communication between vehicles, infrastructure, and traffic-management systems. Many real-world implementations still consider traditional Public Key Infrastructures (PKI) as the underlying trust model and security control. However, there are challenges with the PKI-based security control from a scalability and revocation perspective. Lately, certificateless cryptography has gained research attention, also in conjunction with C-ITSs, making it a new type of security control to be considered. In this study, we use certificateless cryptography as a candidate to investigate factors affecting decisions (not) to adopt new types of security controls, and study its current gaps, key challenges and possible enablers which can influence the industry. We provide a qualitative study with industry specialists in C-ITSs, combined with a literature analysis of the current state of research in certificateless cryptographic in C-ITS. It was found that only 53% of the current certificateless cryptography literature for C-ITSs in 2022–2023 provide laboratory testing of the protocols, and 0% have testing in real-world settings. However, the trend of research output in the field has been increasing linearly since 2016 with more than eight times as many articles in 2022 compared to 2016. Based on our analysis, using a five-phased Innovation-Decision Model, we found that key reasons affecting adoption are: availability of proof-of-concepts, knowledge beyond current best practices, and a strong buy-in from both stakeholders and standardization bodies.
Full article
(This article belongs to the Topic Trends and Prospects in Security, Encryption and Encoding)
►
Show Figures
Open AccessSystematic Review
Abuse of Cloud-Based and Public Legitimate Services as Command-and-Control (C&C) Infrastructure: A Systematic Literature Review
J. Cybersecur. Priv. 2023, 3(3), 558-590; https://doi.org/10.3390/jcp3030027 (registering DOI) - 01 Sep 2023
Abstract
The widespread adoption of cloud-based and public legitimate services (CPLS) has inadvertently opened up new avenues for cyber attackers to establish covert and resilient command-and-control (C&C) communication channels. This abuse poses a significant cybersecurity threat, as it allows malicious traffic to blend seamlessly
[...] Read more.
The widespread adoption of cloud-based and public legitimate services (CPLS) has inadvertently opened up new avenues for cyber attackers to establish covert and resilient command-and-control (C&C) communication channels. This abuse poses a significant cybersecurity threat, as it allows malicious traffic to blend seamlessly with legitimate network activities. Traditional detection systems are proving inadequate in accurately identifying such abuses, emphasizing the urgent need for more advanced detection techniques. In our study, we conducted an extensive systematic literature review (SLR) encompassing the academic and industrial literature from 2008 to July 2023. Our review provides a comprehensive categorization of the attack techniques employed in CPLS abuses and offers a detailed overview of the currently developed detection strategies. Our findings indicate a substantial increase in cloud-based abuses, facilitated by various attack techniques. Despite this alarming trend, the focus on developing detection strategies remains limited, with only 7 out of 91 studies addressing this concern. Our research serves as a comprehensive review of CPLS abuse for the C&C infrastructure. By examining the emerging techniques used in these attacks, we aim to make a significant contribution to the development of effective botnet defense strategies.
Full article
(This article belongs to the Special Issue Cloud Security and Privacy)
►▼
Show Figures
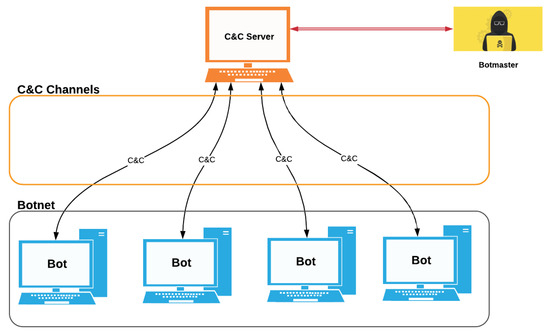
Figure 1
Open AccessArticle
Hybrid Machine Learning-Based Approaches for Feature and Overfitting Reduction to Model Intrusion Patterns
J. Cybersecur. Priv. 2023, 3(3), 544-557; https://doi.org/10.3390/jcp3030026 - 25 Aug 2023
Abstract
An intrusion detection system (IDS), whether as a device or software-based agent, plays a significant role in networks and systems security by continuously monitoring traffic behaviour to detect malicious activities. The literature includes IDSs that leverage models trained to detect known attack behaviours.
[...] Read more.
An intrusion detection system (IDS), whether as a device or software-based agent, plays a significant role in networks and systems security by continuously monitoring traffic behaviour to detect malicious activities. The literature includes IDSs that leverage models trained to detect known attack behaviours. However, such models suffer from low accuracy or high overfitting. This work aims to enhance the performance of the IDS by making a model based on the observed traffic via applying different single and ensemble classifiers and lowering the classifier’s overfitting on a reduced set of features. We implement various feature reduction techniques, including Linear Regression, LASSO, Random Forest, Boruta, and autoencoders on the CSE-CIC-IDS2018 dataset to provide a training set for classifiers, including Decision Tree, Naïve Bayes, neural networks, Random Forest, and XGBoost. Our experiments show that the Decision Tree classifier on autoencoders-based reduced sets of features yields the lowest overfitting among other combinations.
Full article
(This article belongs to the Special Issue Intrusion, Malware Detection and Prevention in Networks)
►▼
Show Figures
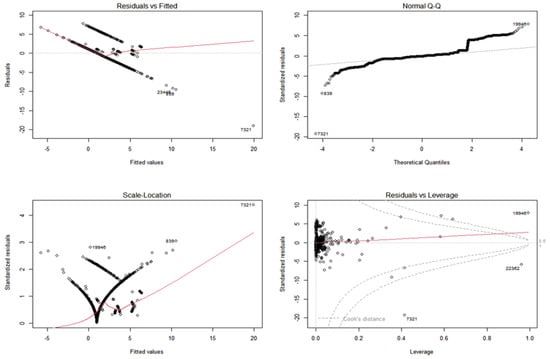
Figure 1
Open AccessReview
Autonomous Vehicles: Sophisticated Attacks, Safety Issues, Challenges, Open Topics, Blockchain, and Future Directions
by
, , , , , , and
J. Cybersecur. Priv. 2023, 3(3), 493-543; https://doi.org/10.3390/jcp3030025 - 05 Aug 2023
Abstract
Autonomous vehicles (AVs), defined as vehicles capable of navigation and decision-making independent of human intervention, represent a revolutionary advancement in transportation technology. These vehicles operate by synthesizing an array of sophisticated technologies, including sensors, cameras, GPS, radar, light imaging detection and ranging (LiDAR),
[...] Read more.
Autonomous vehicles (AVs), defined as vehicles capable of navigation and decision-making independent of human intervention, represent a revolutionary advancement in transportation technology. These vehicles operate by synthesizing an array of sophisticated technologies, including sensors, cameras, GPS, radar, light imaging detection and ranging (LiDAR), and advanced computing systems. These components work in concert to accurately perceive the vehicle’s environment, ensuring the capacity to make optimal decisions in real-time. At the heart of AV functionality lies the ability to facilitate intercommunication between vehicles and with critical road infrastructure—a characteristic that, while central to their efficacy, also renders them susceptible to cyber threats. The potential infiltration of these communication channels poses a severe threat, enabling the possibility of personal information theft or the introduction of malicious software that could compromise vehicle safety. This paper offers a comprehensive exploration of the current state of AV technology, particularly examining the intersection of autonomous vehicles and emotional intelligence. We delve into an extensive analysis of recent research on safety lapses and security vulnerabilities in autonomous vehicles, placing specific emphasis on the different types of cyber attacks to which they are susceptible. We further explore the various security solutions that have been proposed and implemented to address these threats. The discussion not only provides an overview of the existing challenges but also presents a pathway toward future research directions. This includes potential advancements in the AV field, the continued refinement of safety measures, and the development of more robust, resilient security mechanisms. Ultimately, this paper seeks to contribute to a deeper understanding of the safety and security landscape of autonomous vehicles, fostering discourse on the intricate balance between technological advancement and security in this rapidly evolving field.
Full article
(This article belongs to the Special Issue Cybersecurity Risk Prediction, Assessment and Management)
►▼
Show Figures

Figure 1
Open AccessArticle
Deploying Secure Distributed Systems: Comparative Analysis of GNS3 and SEED Internet Emulator
J. Cybersecur. Priv. 2023, 3(3), 464-492; https://doi.org/10.3390/jcp3030024 - 03 Aug 2023
Abstract
►▼
Show Figures
Network emulation offers a flexible solution for network deployment and operations, leveraging software to consolidate all nodes in a topology and utilizing the resources of a single host system server. This research paper investigated the state of cybersecurity in virtualized systems, covering vulnerabilities,
[...] Read more.
Network emulation offers a flexible solution for network deployment and operations, leveraging software to consolidate all nodes in a topology and utilizing the resources of a single host system server. This research paper investigated the state of cybersecurity in virtualized systems, covering vulnerabilities, exploitation techniques, remediation methods, and deployment strategies, based on an extensive review of the related literature. We conducted a comprehensive performance evaluation and comparison of two network-emulation platforms: Graphical Network Simulator-3 (GNS3), an established open-source platform, and the SEED Internet Emulator, an emerging platform, alongside physical Cisco routers. Additionally, we present a Distributed System that seamlessly integrates network architecture and emulation capabilities. Empirical experiments assessed various performance criteria, including the bandwidth, throughput, latency, and jitter. Insights into the advantages, challenges, and limitations of each platform are provided based on the performance evaluation. Furthermore, we analyzed the deployment costs and energy consumption, focusing on the economic aspects of the proposed application.
Full article
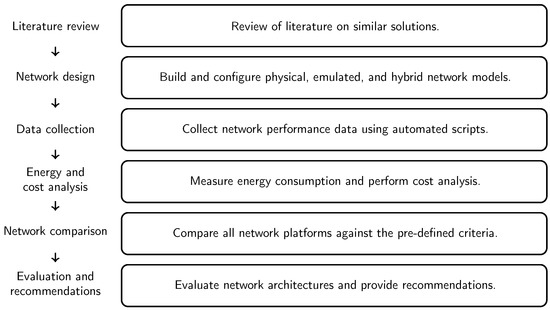
Figure 1
Open AccessArticle
A Deep Learning Approach for Network Intrusion Detection Using a Small Features Vector
J. Cybersecur. Priv. 2023, 3(3), 451-463; https://doi.org/10.3390/jcp3030023 - 03 Aug 2023
Abstract
With the growth in network usage, there has been a corresponding growth in the nefarious exploitation of this technology. A wide array of techniques is now available that can be used to deal with cyberattacks, and one of them is network intrusion detection.
[...] Read more.
With the growth in network usage, there has been a corresponding growth in the nefarious exploitation of this technology. A wide array of techniques is now available that can be used to deal with cyberattacks, and one of them is network intrusion detection. Artificial Intelligence (AI) and Machine Learning (ML) techniques have extensively been employed to identify network anomalies. This paper provides an effective technique to evaluate the classification performance of a deep-learning-based Feedforward Neural Network (FFNN) classifier. A small feature vector is used to detect network traffic anomalies in the UNSW-NB15 and NSL-KDD datasets. The results show that a large feature set can have redundant and unuseful features, and it requires high computation power. The proposed technique exploits a small feature vector and achieves better classification accuracy.
Full article
(This article belongs to the Special Issue Intrusion, Malware Detection and Prevention in Networks)
►▼
Show Figures
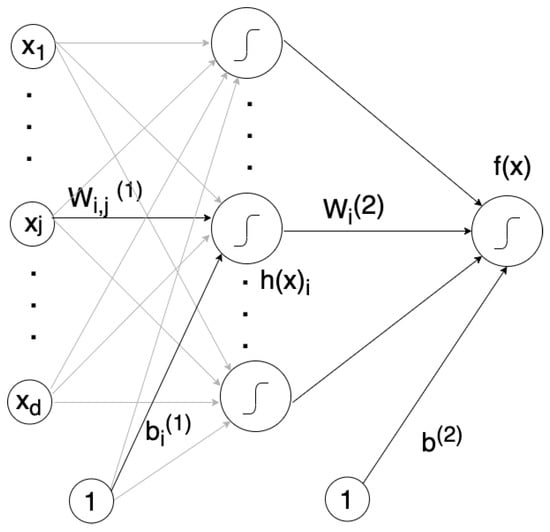
Figure 1
Open AccessArticle
Hourly Network Anomaly Detection on HTTP Using Exponential Random Graph Models and Autoregressive Moving Average
by
and
J. Cybersecur. Priv. 2023, 3(3), 435-450; https://doi.org/10.3390/jcp3030022 - 01 Aug 2023
Abstract
Network anomaly detection solutions can analyze a network’s data volume by protocol over time and can detect many kinds of cyberattacks such as exfiltration. We use exponential random graph models (ERGMs) in order to flatten hourly network topological characteristics into a time series,
[...] Read more.
Network anomaly detection solutions can analyze a network’s data volume by protocol over time and can detect many kinds of cyberattacks such as exfiltration. We use exponential random graph models (ERGMs) in order to flatten hourly network topological characteristics into a time series, and Autoregressive Moving Average (ARMA) to analyze that time series and to detect potential attacks. In particular, we extend our previous method in not only demonstrating detection over hourly data but also through labeling of nodes and over the HTTP protocol. We demonstrate the effectiveness of our method using real-world data for creating exfiltration scenarios. We highlight how our method has the potential to provide a useful description of what is happening in the network structure and how this can assist cybersecurity analysts in making better decisions in conjunction with existing intrusion detection systems. Finally, we describe some strengths of our method, its accuracy based on the right selection of parameters, as well as its low computational requirements.
Full article
(This article belongs to the Special Issue Intrusion, Malware Detection and Prevention in Networks)
►▼
Show Figures
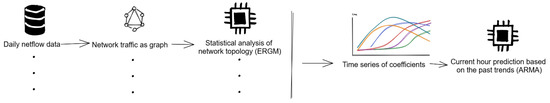
Figure 1
Open AccessArticle
Post-Quantum Authentication in the MQTT Protocol
J. Cybersecur. Priv. 2023, 3(3), 416-434; https://doi.org/10.3390/jcp3030021 - 31 Jul 2023
Abstract
Message Queue Telemetry Transport (MQTT) is a common communication protocol used in the Internet of Things (IoT). MQTT is a simple, lightweight messaging protocol used to establish communication between multiple devices relying on the publish–subscribe model. However, the protocol does not provide authentication,
[...] Read more.
Message Queue Telemetry Transport (MQTT) is a common communication protocol used in the Internet of Things (IoT). MQTT is a simple, lightweight messaging protocol used to establish communication between multiple devices relying on the publish–subscribe model. However, the protocol does not provide authentication, and most proposals to incorporate it lose their lightweight feature and do not consider the future risk of quantum attacks. IoT devices are generally resource-constrained, and postquantum cryptography is often more computationally resource-intensive compared to current cryptographic standards, adding to the complexity of the transition. In this paper, we use the postquantum digital signature scheme CRYSTALS-Dilithium to provide authentication for MQTT and determine what the CPU, memory and disk usage are when doing so. We further investigate another possibility to provide authentication when using MQTT, namely a key encapsulation mechanism (KEM) trick proposed in 2020 for transport level security (TLS). Such a trick is claimed to save up to 90% in CPU cycles. We use the postquantum KEM scheme CRYSTALS-KYBER and compare the resulting CPU, memory and disk usages with traditional authentication. We found that the use of KEM for authentication resulted in a speed increase of 25 ms, a saving of 71%. There were some extra costs for memory but this is minimal enough to be acceptable for most IoT devices.
Full article
(This article belongs to the Section Security Engineering & Applications)
►▼
Show Figures
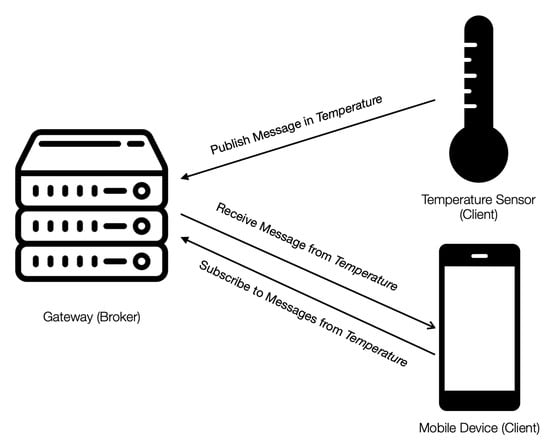
Figure 1
Open AccessArticle
How to Influence Privacy Behavior Using Cognitive Theory and Respective Determinant Factors
by
and
J. Cybersecur. Priv. 2023, 3(3), 396-415; https://doi.org/10.3390/jcp3030020 - 17 Jul 2023
Abstract
Several studies have shown that the traditional way of learning is not optimal when we aim to improve ICT users’ actual privacy behaviors. In this research, we present a literature review of the theories that are followed in other fields to modify human
[...] Read more.
Several studies have shown that the traditional way of learning is not optimal when we aim to improve ICT users’ actual privacy behaviors. In this research, we present a literature review of the theories that are followed in other fields to modify human behavior. Our findings show that cognitive theory and the health belief model present optimistic results. Further, we examined various learning methods, and we concluded that experiential learning is advantageous compared to other methods. In this paper, we aggregate the privacy behavior determinant factors found in the literature and use cognitive theory to synthesize a theoretical framework. The proposed framework can be beneficial to educational policymakers and practitioners in institutions such as public and private schools and universities. Also, our framework provides a fertile ground for more research on experiential privacy learning and privacy behavior enhancement.
Full article
(This article belongs to the Section Privacy)
►▼
Show Figures
Figure 1
Open AccessFeature PaperArticle
VEDRANDO: A Novel Way to Reveal Stealthy Attack Steps on Android through Memory Forensics
J. Cybersecur. Priv. 2023, 3(3), 364-395; https://doi.org/10.3390/jcp3030019 - 10 Jul 2023
Abstract
The ubiquity of Android smartphones makes them targets of sophisticated malware, which maintain long-term stealth, particularly by offloading attack steps to benign apps. Such malware leaves little to no trace in logs, and the attack steps become difficult to discern from benign app
[...] Read more.
The ubiquity of Android smartphones makes them targets of sophisticated malware, which maintain long-term stealth, particularly by offloading attack steps to benign apps. Such malware leaves little to no trace in logs, and the attack steps become difficult to discern from benign app functionality. Endpoint detection and response (EDR) systems provide live forensic capabilities that enable anomaly detection techniques to detect anomalous behavior in application logs after an app hijack. However, this presents a challenge, as state-of-the-art EDRs rely on device and third-party application logs, which may not include evidence of attack steps, thus prohibiting anomaly detection techniques from exposing anomalous behavior. While, theoretically, all the evidence resides in volatile memory, its ephemerality necessitates timely collection, and its extraction requires device rooting or app repackaging. We present VEDRANDO, an enhanced EDR for Android that accomplishes (i) the challenge of timely collection of volatile memory artefacts and (ii) the detection of a class of stealthy attacks that hijack benign applications. VEDRANDO leverages memory forensics and app virtualization techniques to collect timely evidence from memory, which allows uncovering attack steps currently uncollected by the state-of-the-art EDRs. The results showed that, with less than 5% CPU overhead compared to normal usage, VEDRANDO could uniquely collect and fully reconstruct the stealthy attack steps of ten realistic messaging hijack attacks using standard anomaly detection techniques, without requiring device or app modification.
Full article
(This article belongs to the Special Issue Cyber Security and Digital Forensics)
►▼
Show Figures
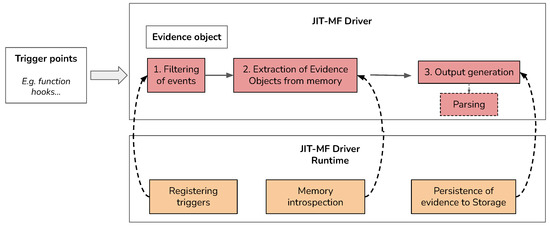
Figure 1
Open AccessArticle
Power-Based Side-Channel Attacks on Program Control Flow with Machine Learning Models
J. Cybersecur. Priv. 2023, 3(3), 351-363; https://doi.org/10.3390/jcp3030018 - 07 Jul 2023
Abstract
The control flow of a program represents valuable and sensitive information; in embedded systems, this information can take on even greater value as the resources, control flow, and execution of the system have more constraints and functional implications than modern desktop environments. Early
[...] Read more.
The control flow of a program represents valuable and sensitive information; in embedded systems, this information can take on even greater value as the resources, control flow, and execution of the system have more constraints and functional implications than modern desktop environments. Early works have demonstrated the possibility of recovering such control flow through power-based side-channel attacks in tightly constrained environments; however, they relied on meaningful differences in computational states or data dependency to distinguish between states in a state machine. This work applies more advanced machine learning techniques to state machines which perform identical operations in all branches of control flow. Complete control flow is recovered with 99% accuracy even in situations where 97% of work is outside of the control flow structures. This work demonstrates the efficacy of these approaches for recovering control flow information; continues developing available knowledge about power-based attacks on program control flow; and examines the applicability of multiple standard machine learning models to the problem of classification over power-based side-channel information.
Full article
(This article belongs to the Collection Machine Learning and Data Analytics for Cyber Security)
►▼
Show Figures
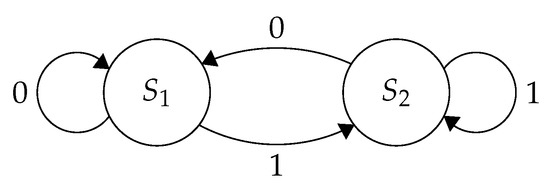
Figure 1
Open AccessArticle
A Dynamic and Adaptive Cybersecurity Governance Framework
J. Cybersecur. Priv. 2023, 3(3), 327-350; https://doi.org/10.3390/jcp3030017 - 30 Jun 2023
Abstract
►▼
Show Figures
Cybersecurity protects cyberspace from a wide range of cyber threats to reduce overall business risk, ensure business continuity, and maximize business opportunities and return on investments. Cybersecurity is well achieved by using appropriate sets of security governance frameworks. To this end, various Information
[...] Read more.
Cybersecurity protects cyberspace from a wide range of cyber threats to reduce overall business risk, ensure business continuity, and maximize business opportunities and return on investments. Cybersecurity is well achieved by using appropriate sets of security governance frameworks. To this end, various Information Technology (IT) and cybersecurity governance frameworks have been reviewed along with their benefits and limitations. The major limitations of the reviewed frameworks are; they are complex and have complicated structures to implement, they are expensive and require high skill IT and security professionals. Moreover, the frameworks require many requirement checklists for implementation and auditing purposes and a lot of time and resources. To fill the limitations mentioned above, a simple, dynamic, and adaptive cybersecurity governance framework is proposed that provides security related strategic direction, ensures that security risks are managed appropriately, and ensures that organizations’ resources are utilized optimally. The framework incorporated different components not considered in the existing frameworks, such as research and development, public-private collaboration framework, regional and international cooperation framework, incident management, business continuity, disaster recovery frameworks, and compliance with laws and regulations. Moreover, the proposed framework identifies and includes some of the existing frameworks’ missed and overlapped components, processes, and activities. It has nine components, five activities, four outcomes, and seven processes. Performance metrics, evaluation, and monitoring techniques are also proposed. Moreover, it follows a risk based approach to address the current and future technology and threat landscapes. The design science research method was used in this research study to solve the problem mentioned. Using the design science research method, the problem was identified. Based on the problem, research objectives were articulated; the objective of this research was solved by developing a security governance framework considering different factors which were not addressed in the current works. Finally, performance metrics were proposed to evaluate the implementation of the governance framework.
Full article
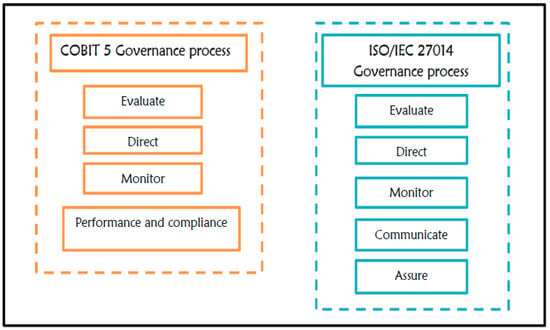
Figure 1
Open AccessArticle
Assessing the Security and Privacy of Baby Monitor Apps
J. Cybersecur. Priv. 2023, 3(3), 303-326; https://doi.org/10.3390/jcp3030016 - 29 Jun 2023
Abstract
Emerging technologies in video monitoring solutions seriously threaten personal privacy, as current technologies hold the potential for total surveillance. These concerns apply in particular to baby monitor solutions incorporating mobile applications due to the potential privacy impact of combining sensitive video recordings with
[...] Read more.
Emerging technologies in video monitoring solutions seriously threaten personal privacy, as current technologies hold the potential for total surveillance. These concerns apply in particular to baby monitor solutions incorporating mobile applications due to the potential privacy impact of combining sensitive video recordings with access to the vast amount of private data on a cell phone. Therefore, this study extends the state of privacy research by assessing the security and privacy of popular baby monitor apps. We analyze network security measures that aim to protect baby monitoring streams, evaluate the corresponding privacy policies, and identify privacy leaks by performing network traffic analysis. Our results point to several problems that may compromise user privacy. We conclude that our methods can support the evaluation of the security and privacy of video surveillance solutions and discuss how to improve the protection of user data.
Full article
(This article belongs to the Special Issue Privacy-Enhancing Technologies for User Systems to Foster a More Ethical E-Society)
►▼
Show Figures
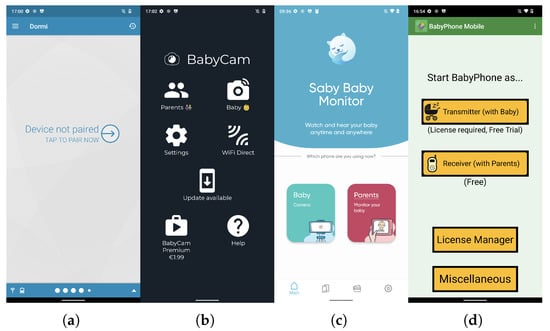
Figure 1
Open AccessArticle
Modeling Intruder Reconnaissance Behavior through State Diagrams to Support Defensive Deception
J. Cybersecur. Priv. 2023, 3(2), 275-302; https://doi.org/10.3390/jcp3020015 - 14 Jun 2023
Abstract
Active reconnaissance is the primary source of information gathering about the infrastructure of a target network for intruders. Its main functions are host discovery and port scanning, the basic techniques of which are thoroughly analyzed in the present paper. The main contribution of
[...] Read more.
Active reconnaissance is the primary source of information gathering about the infrastructure of a target network for intruders. Its main functions are host discovery and port scanning, the basic techniques of which are thoroughly analyzed in the present paper. The main contribution of the paper is the definition of a modeling approach regarding (a) all possible intruder actions, (b) full or partial knowledge of the intruder’s preferred methodology, and (c) the topology of the target network. The result of the modeling approach, which is based on state diagrams, is the extraction of a set of all probable paths that the intruder may follow. On top of this, a number of relevant metrics are calculated to enable the dynamic assessment of the risk to specific network assets according to the point on the paths at which the intruder is detected. The proposed methodology aims to provide a robust model that can enable the efficient and automated application of deception techniques to protect a given network. A series of experiments has also been performed to assess the required resources for the modeling approach when applied in real-world applications and provide the required results with bearable overhead to enable the online application of deception measures.
Full article
(This article belongs to the Section Security Engineering & Applications)
►▼
Show Figures

Figure 1
Open AccessArticle
A Lesson for the Future: Will You Let Me Violate Your Privacy to Save Your Life?
by
and
J. Cybersecur. Priv. 2023, 3(2), 259-274; https://doi.org/10.3390/jcp3020014 - 14 Jun 2023
Abstract
COVID-19 was an unprecedented pandemic that changed the lives of everyone. To handle the virus’s rapid spread, governments and big tech companies, such as Google and Apple, implemented Contact Tracing Applications (CTAs). However, the response by the public was different in each country.
[...] Read more.
COVID-19 was an unprecedented pandemic that changed the lives of everyone. To handle the virus’s rapid spread, governments and big tech companies, such as Google and Apple, implemented Contact Tracing Applications (CTAs). However, the response by the public was different in each country. While some countries mandated downloading the application for their citizens, others made it optional, revealing contrasting patterns to the spread of COVID-19. In this study, in addition to investigating the privacy and security of the Canadian CTA, COVID Alert, we aim to disclose the public’s perception of these varying patterns. Additionally, if known of the results of other nations, would Canadians sacrifice their freedoms to prevent the spread of a future pandemic? Hence, a survey was conducted, gathering responses from 154 participants across Canada. Next, we questioned the participants regarding the COVID-19 pandemic and their knowledge and opinion of CTAs before presenting our findings regarding other countries. After showing our results, we then asked the participants their views of CTAs again. The arrangement of the preceding questions, the findings, and succeeding questions to identify whether Canadians’ opinions on CTAs would change, after presenting the proper evidence, were performed. Among all of our findings, there is a clear difference between before and after the findings regarding whether CTAs should be mandatory, with 34% of participants agreeing before and 56% agreeing afterward. This hints that all the public needed was information to decide whether or not to participate. In addition, this exposes the value of transparency and communication when persuading the public to collaborate. Finally, we offer three recommendations on how governments and health authorities can respond effectively in a future pandemic and increase the adoption rate for CTAs to save more lives.
Full article
(This article belongs to the Special Issue Privacy-Enhancing Technologies for User Systems to Foster a More Ethical E-Society)
►▼
Show Figures
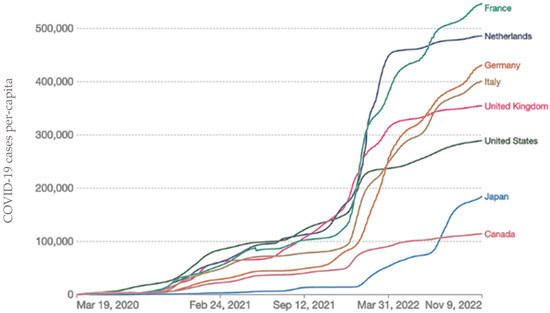
Figure 1
Open AccessReview
Deep Learning and Machine Learning, Better Together Than Apart: A Review on Biometrics Mobile Authentication
J. Cybersecur. Priv. 2023, 3(2), 227-258; https://doi.org/10.3390/jcp3020013 - 13 Jun 2023
Abstract
►▼
Show Figures
Throughout the past several decades, mobile devices have evolved in capability and popularity at growing rates while improvement in security has fallen behind. As smartphones now hold mass quantities of sensitive information from millions of people around the world, addressing this gap in
[...] Read more.
Throughout the past several decades, mobile devices have evolved in capability and popularity at growing rates while improvement in security has fallen behind. As smartphones now hold mass quantities of sensitive information from millions of people around the world, addressing this gap in security is crucial. Recently, researchers have experimented with behavioral and physiological biometrics-based authentication to improve mobile device security. Continuing the previous work in this field, this study identifies popular dynamics in behavioral and physiological smartphone authentication and aims to provide a comprehensive review of their performance with various deep learning and machine learning algorithms. We found that utilizing hybrid schemes with deep learning features and deep learning/machine learning classification can improve authentication performance. Throughout this paper, the benefits, limitations, and recommendations for future work will be discussed.
Full article
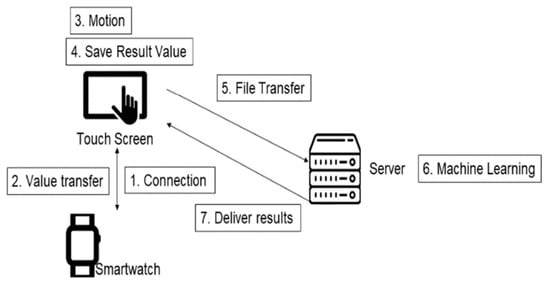
Figure 1
Open AccessArticle
Mitigating IoT Privacy-Revealing Features by Time Series Data Transformation
J. Cybersecur. Priv. 2023, 3(2), 209-226; https://doi.org/10.3390/jcp3020012 - 18 May 2023
Abstract
As the Internet of Things (IoT) continues to expand, billions of IoT devices are now connected to the internet, producing vast quantities of data. Collecting and sharing this data has become crucial to improving IoT technologies and developing new applications. However, the publication
[...] Read more.
As the Internet of Things (IoT) continues to expand, billions of IoT devices are now connected to the internet, producing vast quantities of data. Collecting and sharing this data has become crucial to improving IoT technologies and developing new applications. However, the publication of privacy-preserving IoT traffic data is exceedingly challenging due to the various privacy concerns surrounding users, IoT networks, and devices. In this paper, we propose a data transformation method aimed at safeguarding the privacy of IoT devices by transforming time series datasets. Based on our measurements, we have found that the transformed datasets retain the intrinsic value of the original IoT data and maintains data utility. This approach will enable non-expert data owners to better understand and evaluate the potential device-level privacy risks associated with their IoT data while simultaneously offering a reliable solution to mitigate their concerns about privacy violations.
Full article
(This article belongs to the Special Issue Intrusion, Malware Detection and Prevention in Networks)
►▼
Show Figures
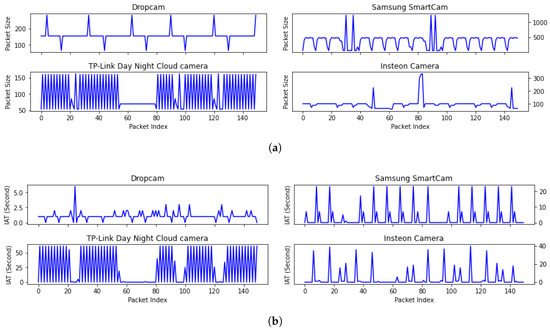
Figure 1
Open AccessArticle
Cybersecurity in a Large-Scale Research Facility—One Institution’s Approach
by
, , , , , , and
J. Cybersecur. Priv. 2023, 3(2), 191-208; https://doi.org/10.3390/jcp3020011 - 16 May 2023
Abstract
A cybersecurity approach for a large-scale user facility is presented—utilizing the National High Magnetic Field Laboratory (NHMFL) at Florida State University (FSU) as an example. The NHMFL provides access to the highest magnetic fields for scientific research teams from a range of disciplines.
[...] Read more.
A cybersecurity approach for a large-scale user facility is presented—utilizing the National High Magnetic Field Laboratory (NHMFL) at Florida State University (FSU) as an example. The NHMFL provides access to the highest magnetic fields for scientific research teams from a range of disciplines. The unique challenges of cybersecurity at a widely accessible user facility are showcased, and relevant cybersecurity frameworks for the complex needs of a user facility with industrial-style equipment and hazards are discussed, along with the approach for risk identification and management, which determine cybersecurity requirements and priorities. Essential differences between information technology and research technology are identified, along with unique requirements and constraints. The need to plan for the introduction of new technology and manage legacy technologies with long usage lifecycles is identified in the context of implementing cybersecurity controls rooted in pragmatic decisions to avoid hindering research activities while enabling secure practices, which includes FAIR (findable, accessible, interoperable, and reusable) and open data management principles. The NHMFL’s approach to FAIR data management is presented. Critical success factors include obtaining resources to implement and maintain necessary security protocols, interdisciplinary and diverse skill sets, phased implementation, and shared allocation of NHMFL and FSU responsibilities.
Full article
(This article belongs to the Topic Cyber Security and Critical Infrastructures)
►▼
Show Figures
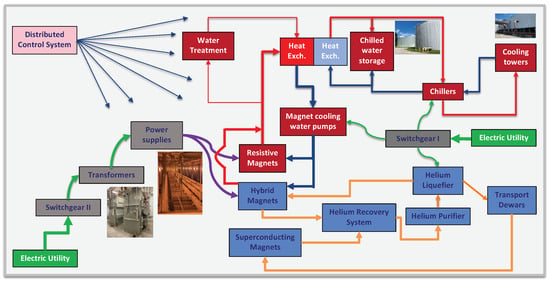
Figure 1
Open AccessFeature PaperReview
Cybersecurity for AI Systems: A Survey
J. Cybersecur. Priv. 2023, 3(2), 166-190; https://doi.org/10.3390/jcp3020010 - 04 May 2023
Abstract
Recent advances in machine learning have created an opportunity to embed artificial intelligence in software-intensive systems. These artificial intelligence systems, however, come with a new set of vulnerabilities making them potential targets for cyberattacks. This research examines the landscape of these cyber attacks
[...] Read more.
Recent advances in machine learning have created an opportunity to embed artificial intelligence in software-intensive systems. These artificial intelligence systems, however, come with a new set of vulnerabilities making them potential targets for cyberattacks. This research examines the landscape of these cyber attacks and organizes them into a taxonomy. It further explores potential defense mechanisms to counter such attacks and the use of these mechanisms early during the development life cycle to enhance the safety and security of artificial intelligence systems.
Full article
(This article belongs to the Collection Machine Learning and Data Analytics for Cyber Security)
►▼
Show Figures
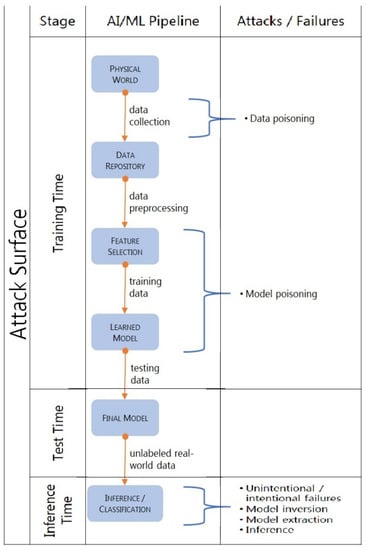
Figure 1
Open AccessFeature PaperArticle
Investigating the Privacy and Security of the SimpliSafe Security System on Android and iOS
J. Cybersecur. Priv. 2023, 3(2), 145-165; https://doi.org/10.3390/jcp3020009 - 07 Apr 2023
Abstract
The emergence of the Internet of Things technologies and the increase and convenience of smart home devices have contributed to the growth of self-installed home security systems. While home security devices have become more accessible and can help users monitor and secure their
[...] Read more.
The emergence of the Internet of Things technologies and the increase and convenience of smart home devices have contributed to the growth of self-installed home security systems. While home security devices have become more accessible and can help users monitor and secure their homes, they can also become targets of cyberattacks and/or witnesses of criminal activities, hence sources of forensic evidence. To date, there is little existing literature on forensic analysis and the security and privacy of home security systems. In this paper, we seek to better understand and assess the forensic artifacts that can be extracted, the security and privacy concerns around the use of home security devices, and the challenges forensic investigators might encounter, by performing a comprehensive investigation of the SimpliSafe security system. We investigated the interaction of the security system with the SimpliSafe companion app on both Android and iOS devices. We analyzed the network traffic as the user interacts with the system to identify any security or privacy concerns. Our method can help investigators working on other home security systems, and our findings can further help developers to improve the confidentiality and privacy of user data in home security devices and their applications.
Full article
(This article belongs to the Special Issue Cyber Security and Digital Forensics)
►▼
Show Figures

Figure 1
Highly Accessed Articles
Latest Books
E-Mail Alert
News
Topics
Topic in
Applied Sciences, Cryptography, JCP, JSAN, Sci, Symmetry
Trends and Prospects in Security, Encryption and Encoding
Topic Editors: Ki-Hyun Jung, Luis Javier García VillalbaDeadline: 29 February 2024
Topic in
Electronics, JCP, Mathematics, Sustainability, Remote Sensing
Recent Advances in Security, Privacy, and Trust
Topic Editors: Jun Feng, Changqing Luo, Mamoun AlazabDeadline: 31 December 2025

Conferences
Special Issues
Special Issue in
JCP
Cyber Security and Digital Forensics
Guest Editors: Mario Antunes, Carlos RabadãoDeadline: 20 September 2023
Special Issue in
JCP
Cybersecurity Risk Prediction, Assessment and Management
Guest Editors: Gahangir Hossain, Ibrahim Lazrig, Murray JennexDeadline: 30 September 2023
Special Issue in
JCP
Secure Software Engineering
Guest Editor: Hossein SaiedianDeadline: 31 October 2023
Special Issue in
JCP
Multimedia Security and Privacy
Guest Editor: Arslan MunirDeadline: 10 December 2023
Topical Collections
Topical Collection in
JCP
Intelligent Security and Privacy Approaches against Cyber Threats
Collection Editor: Nour Moustafa
Topical Collection in
JCP
Machine Learning and Data Analytics for Cyber Security
Collection Editors: Phil Legg, Giorgio Giacinto